How to Stop Someone from Spying on My Cell Phone? [With Preventions]
Technology brings convenience to our lives and leaves us with no privacy at all. Are you in panic all day long for being monitored by others when you enter your bank card password, take selfies, or browse private content on your mobile phone? It is very easy for hackers to use surveillance software to monitor your mobile phone in the big data era.
However, you don't have to worry. After reading this article, you will know how to stop someone from spying on a cell phone in a few simple ways.

It isn't easy to detect spyware on your smartphone since it usually operates stealthily. However, there are suspicious signs that could signal when someone is spying on you.
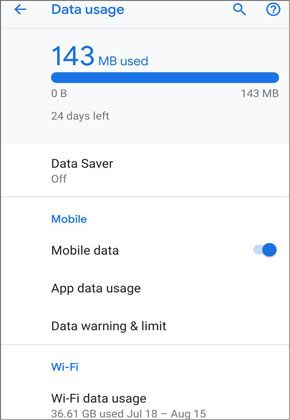
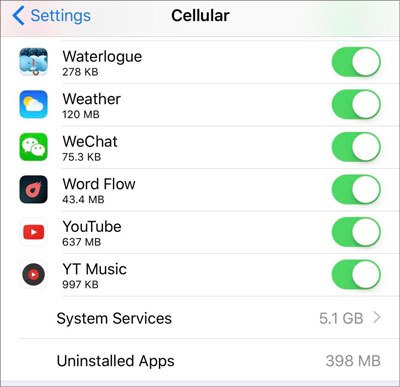
The cellular data consumption on your device may be an obvious signal for spyware running in the background. Lower-quality spyware will transmit as much data as possible from your device to the home base, exhausting excessive cellular data.
Therefore, you'd better keep an eye on the monthly data usage and the sudden peaks of your device. You can contact your carrier to check the data usage or check it yourself on your device.
To check the cellular data usage on Android devices:
To check cellular data usage on iPhone or iPad:
Although phone battery performance decreases with age or the usage frequency, the instant battery drainage will not be so simple. If the spyware works unceasingly, it will unusually drain the battery rather than gradually degrade.
So, if you notice a sudden change in battery performance, check whether the newly installed or upgraded apps on your device are accountable. Then you may find the truth behind the phenomenon.

Your smartphone will light up when you receive a phone call, message, or notification. However, the device screen should not be lit for no reason when in Standby mode.
Suppose you hear unexpected sounds or noises while your device lights up without new messages or notifications. In that case, your device may get tapped.
Does your phone reboot randomly without touching it? If yes, someone may have illegally remote admin access to your device at his will and obtain your data, or there are system bugs or incompatible apps on your device.
You can install and run a reliable antivirus app for Android to scan and protect your device. iOS users can fix the iPhone boot loop in ten methods.

Your smartphone may also get monitored if the battery temperature heats up without running heavy apps or when not in use. Besides, if the phone's processing speed drops suddenly, the spyware may sneakily run in the background.
Do you hear any odd noise or buzz while making a phone call? If the answer is positive, recall whether it starts from the beginning or just suddenly.
If the spyware eavesdrops on your phone calls, it will create strange sounds during calls, like white noise, crackles, beeps, and echoes. Even if bad reception can give rise to such interference, you'd better check your device for any distrustful apps or activities.

If you have ever received any messages with strange characters or your friends or family members have received offensive or creepy messages from you, the spyware may have existed on your phone. SMS worms will send text messages with malicious links embedded in them. If you tap the link, the virus will quickly infect your phone.
But iPhone will not easily get infected with such links due to the strengthened iOS security system. Thus, you can install the security software on your Android phone to safeguard your device.
Your smartphone will shut down the active processes like a computer before powering itself off or rebooting and occasionally hang up the shutdown process. This issue can happen to any device. But if you notice that it happens more often or takes prolonged than usual, maybe the spyware is working in the background.
Apart from slowing down the shutdown process, spyware will also prevent your phone from rebooting or shutting down completely. However, a harmless app may misbehave like this. Watch out for your phone if this phenomenon begins abruptly or happens more often than before.
![]()
Usually, high-end smartphones manufactured in the last three years run fast without showing many performance issues in daily use. But if you find your phone becomes lagged, much worse than before, or suddenly runs out of storage space, the spyware may already run on it.
Anyway, it isn't easy to tell with low-end or older handsets. If you are very familiar with your device's performance, maybe you can tell if it goes wrong.
Getting your phone monitored by someone will cause a lot of trouble to you, including:
How to block spying on my cell phone? Don't panic if you find someone spying on your phone. The following tips will stop spying on your smartphone easily.
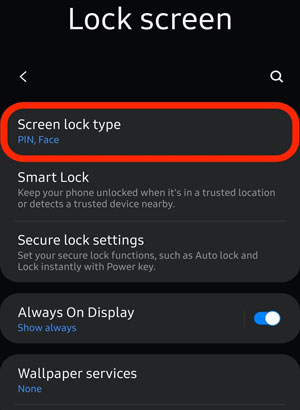
Believe it or not, phone spying is more likely to be conducted by people around us who know your phone passcode rather than anonymous hackers. So, changing the passcode will stop anyone from accessing your phone or installing spyware that quietly steals your pictures, emails, passwords, or chats history.
When changing a passcode, ensure to select a strong code with at least six characters and don't use any easy-to-guess password, like date of birth, 123456, favorite singer's name, etc. If possible, use biometric features like Face ID or Touch ID.
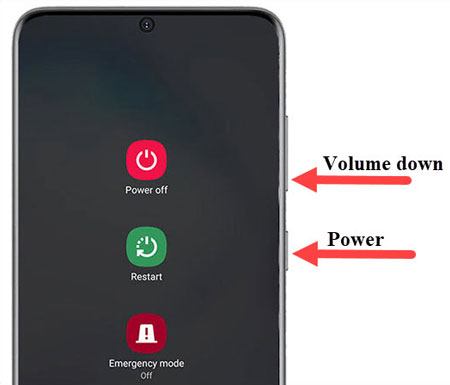
You can reboot your smartphone if it is constantly on. In many cases, restarting your phone stops the spyware from monitoring your device.
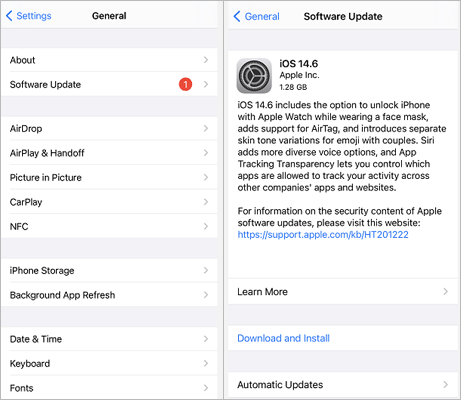
Another simple way to stop the nightmare is by updating the operating system and app version. As some hacking tools can easily intrude the older software version or outdated apps, many Android and iOS manufacturers regularly release the latest updates to protect cell phones from spying.
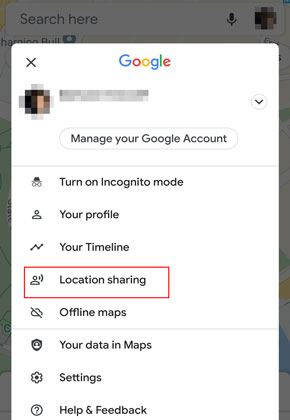
A hacker does not need to install spyware to monitor your location. Some pre-installed apps can share your location to another device in one click, like Google Maps, Apple's Find My, etc.
Therefore, you can check if you have enabled the Location Share feature in either of these apps.
To stop location share in Google Maps on Android:
To stop location share in Find My iPhone/iPad/iPod:

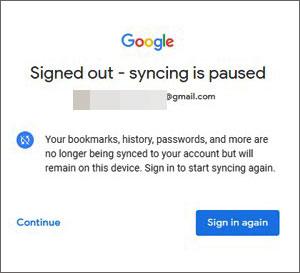
Someone may also track your browsing history and passwords you've saved across the Google Chrome browser app. Consequently, changing the Google Chrome account may solve the problem.
Some spyware will connect your device data, access your GPS location, use your microphone, and even cameras when they don't need to. At this moment, you can manually check this by reviewing permissions in Settings on your Android or iOS devices.
If you have used VPN before, you will know that it encrypts the online resources on your phone by changing to different locations, including social media, websites, or email accounts. Hence, using a reputable VPN will stop someone from eavesdropping on your online activity. However, you should also know that a VPN cannot give you complete protection.
Only the system core applications will load in Safe mode. As a result, you can boot your Android device into Safe mode to stop spyware on your device.

You can also enable two-factor authentication to protect your accounts from being targeted. In doing so, anyone who logs in to your account will need a special code sent to you by message, even if they know your username and password.
Click here to know how to enable two-factor authentication for Apple ID on iPhone and Google account on Android.
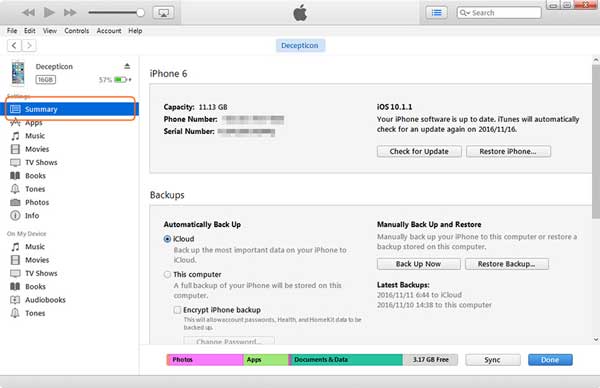
Resetting your device to factory settings deletes all the third-party software, including spyware. Before starting with the following steps, back up your iPhone or Android first to avoid data loss.
To factory reset Android devices:
To factory reset iPhone:
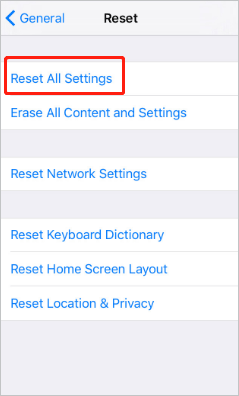
Or,
Additionally, you can remove the spyware from your iPhone or Android devices by using an anti-spyware app. There are various such apps in the market, and below are some of them that have earned a good reputation.
Location Changer is the best mock location app on iOS and Android devices. With this app, you can easily change the location to anywhere globally and use the joystick to fake GPS movement. And it works with many location-based apps, platforms, and AR games.
The key features of Location Changer:
* Fake GPS location on your Android/iOS devices freely.
* Plan a route to move around with customized speed.
* Use the joystick to mock GPS movement.
* Support different location-based apps, AR games, and social platforms, such as WhatsApp, Snapchat, Facebook, Tinder, etc.
Follow these steps to use Location Changer to change your Android or iOS location:
01Download and install Location Changer on your computer. Launch the program and click Get Started to proceed.
02Use a USB cable to connect your phone to the computer. For Android devices, make sure USB debugging is turned on; for iPhone, tap Trust This Computer when the prompt appears.
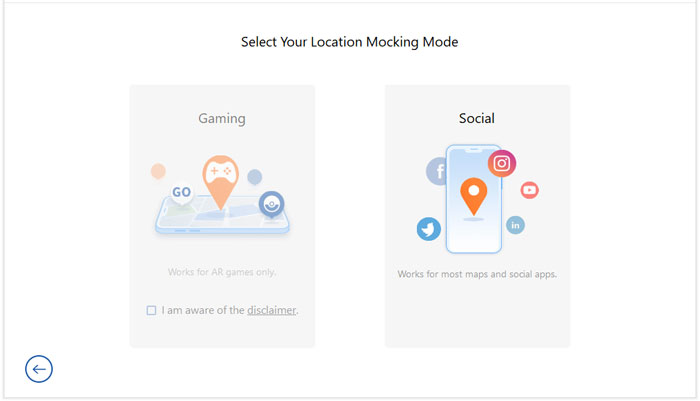
03After the device is recognized, select a mode that fits your needs: Gaming Mode or Social Mode.
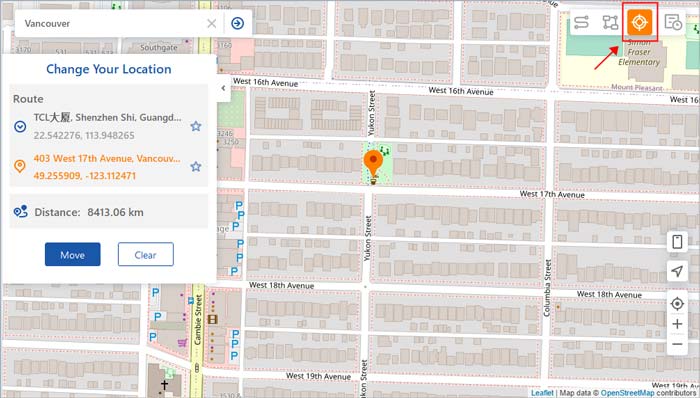
04Type your desired location in the search box or browse the map to pick a destination. Then click Move to update your device's GPS location instantly.
Once finished, all location-based apps on your phone will use the newly set virtual location.
How to prevent spyware on your cell phone? Or, how can I protect my phone from spyware in the future? Just refer to the following methods.
Lock your phone with a strong password, fingerprint, PIN, or set a biometric feature on your device like Face ID or Touch ID. Also, it would be helpful if you turned on the app authentication before installation.

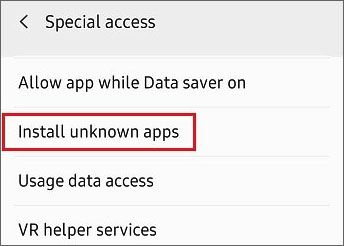
On iPhone, you can install apps with a good user foundation from the App Store. On Android, you can disable the install apps from unknown sources option. Also, be careful with calculators, free VPN apps, and other simple apps, which may quickly combine as a Trojan horse.
As mentioned above, odd messages with links will get your device infected with viruses or spyware. So, check twice before clicking any links and avoid providing your bank account password unhesitatingly.
Do not set too simple passwords, like your date of birth, pet's name, phone number, favorite singer's name, etc. Try to set a complex one that includes uppercases, lowercases, numbers, and special characters and is easy to remember for you.
A jailbroken or rooted device is vulnerable to malware or spyware. Consequently, you'd better never jailbreak or root your smartphone.

Why do almost all phone manufacturers update the operating system periodically? In fact, OS updates fix bugs and improve security performance. An iOS update will bring your phone under Apple's protection even if it has been jailbroken previously.
Some apps may require extra permissions to your position, camera, microphone, or contacts that you even think it's unnecessary, especially on Android devices. For example, some third-party Radio apps ask contacts permission groundlessly. In this case, you should refuse.
Try to reduce people who can access your phone and only allow the trusted ones to use your phone. It will be much tougher to install spyware without physical access to your device.
Don't connect to any public Wi-Fi network when you are out since a hacker may easily control your phone over a fake public Wi-Fi network. Once you connect your phone to it, it will spy on your device without difficulty. You can use a trustworthy VPN to connect to public Wi-Fi to reduce risks.
Switching off Wi-Fi and Bluetooth on your device when not in use protects your device from connecting to a non-secure Wi-Fi or Bluetooth nearby. As a consequence, it will greatly decrease the rate of being hacked.

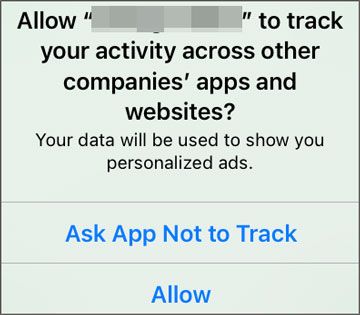
App companies may track your phone data to target ads to you. To avoid monitoring your information, you can limit or opt-out of the ad tracking.
Additional Security Tips for Android:
No one wants to expose their privacy and activities to anyone else. This post teaches you how to stop someone from spying on your cell phone and figure out if someone is spying on your phone and step by step. Moreover, it also tells you effective ways to avoid spyware on your device. You can follow our guide to secure your device accordingly. Additionally, if you are concerned about location tracking, using tools like Location Changer to modify your GPS location can also help enhance your privacy protection.
If you want to know more about data/device security techniques, let us know in the comments.
Related Articles:
How to Change iPhone/iPad Location without Jailbreak in 4 Cost-effective Ways?
How to Change Location on Facebook Marketplace? 4 Simple Ways You Never Know
How to Change Your Location on Snapchat Map on iPhone and Android? (Complete Guide)